The dark web is a part of the internet that you only step into with a specific tool (Tormore on this later in the article). Though people usually think of dark websites as the wrong online placethat’s not the complete truth. To really understand the dark webyou have to look at both sides of the coin. Yesthe underground internet world is rife with everything badbut it also hosts positive elements. It then depends on youas the userhow you surf the dark world.
If you know the right websitesyou can easily access a tremendous amount of informationincluding research articlesnews storiesand more.
This article lists some of the best dark web websites you can visit securely. Some of these sites are very helpful (but unseen as Google doesn’t show them)while others are just for fun.
Please note: This article is solely for the educational and information purposes. It has onion links you cannot access with regular browsers like ChromeFirefoxEdgeor Safari. You will need the Tor browser to access these links and the other (hidden) internetthe dark web. Alsouse a stealth VPN like NordVPN and a dependable antivirus like TotalAV or Bitdefender to double your security while navigating dark web resources if you choose to access them.
10 best Tor sites available on the dark web – Quick list
Running late? Here’s a list of the best Onion and Tor sites in 2026:
- DuckDuckGo: One of the best privacy-focused search engines that does not use trackers and collect your personal data.
- The Hidden Wiki: It is like Wikipedia for the dark webwith the biggest directory of onion services and links.
- Awazon Market: A dark web marketplace that lets people sell and purchase illicit goods and services (mostly).
- ProPublica: An investigative media site and platform that publishes provoking pieces on a wide range of topics related to dark web newsfrom finance to politics.
- Vortex: It’s a hidden internet e-commerce market that security researchers closely watch for its escrow system and the wide range of illicit goods it hosts.
- Tenebris: This is a decentralized forum on the dark web where you can ask any question you like without getting censored.
- OnionFind: A useful dark web search engine that allows you to search incredibly detailed queries.
- Facebook: This is a version of Facebook’s onion portalwhich was developed to help people in repressive regimes access it.
- SecureDrop: Designed for whistleblowers to share information with journalists securely and anonymously.
- BBC Tor Mirror: A special BBC .onion site to offer access to its content in countries with heavy online censorship.
Caution: Safety comes first when visiting dark web links
If you choose to visit the dark webyou must take the necessary measures to protect your privacy and security. This includes using an anonymous browser like Tora VPN to encrypt your connectionan antivirus for protection against malware (we recommend TotalAV)and generally being careful not to reveal personal information.
Whether you’re a researchera security professionalor just curiousdark web intelligence helps you separate the useful from the dangerous. That’s exactly what this guide aims to deliver.
In additionknow that while accessing the dark web is legal in most countriesengaging in illegal activities (buying or selling contrabandhacking servicesetc.) is illegal everywhere. You should be aware that law enforcement agencies may be monitoring the dark web and that visiting certain websites or engaging in illegal activities can result in criminal charges. You can also check out this ultimate dark web safety guide to browse safely.
Best dark web sites 2026 – Detailed list

It is possible to navigate the dark web even though it doesn’t host user-friendly onion search engines. Thankfullysome useful sites can help you circumnavigate the dark web landscape as you search for the best content.
Belowwe list some of them. You can choose the best darknet (.onion) website that suits you and start surfing. Howeverremember you must use the Tor browser to access them. For safer browsingit is highly recommended to also use a VPN and antivirus software.
1. DuckDuckGo

- Direct link: https://duckduckgogg42xjoc72x3sjasowoarfbgcmvfimaftt6twagswzczad.onion/
DuckDuckGo is the most popular private search engine. Unlike other search enginesit does not collect or share the web activities and personal data of users. Luckilyit is also available on the surface web.
It is an excellent option if you want to surf the web anonymously. Even without monitoring your browsing activitiesDuckDuckGo will offer decent answers to your questions.
You can also use it within the dark webas it has .onion links. It will offer you an additional layer of encryption to access the deep parts of the internet.
2. The Hidden Wiki
- Direct link: http://zqktlwi4fecvo6ri.onion/wiki/index.php/Main_Page | https://onionwiki.com/
The Hidden Wiki is a good way to start entering the dark web. It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web.
Howeveryou have to be careful with the links you click. Since Hidden Wiki maintains all kinds of websitesensure you don’t open something you don’t want to see. For exampleit has a reputation for hosting pedophile sites.
Moreoverdue to its popularitymany copycats of the Hidden Wiki exist. So don’t be surprised if you encounter different versions that claim to be genuineand be very careful.
Talking about copycats and potential risksdue to its high risk and low signal-to-noise ratio for legitimate contentwe advise beginners and privacy-conscious users to avoid The Hidden Wiki. Safermore curated directories exist. If you must explore sites like The Hidden Wikido so with extreme skepticismnever download filesnever enter personal infoand never send cryptocurrency to unknown sites. Assume most links are malicious or illegal.
3. Awazon Market
- Direct link 1: awazone7gyw54yau4vb6gvcac4yhnhcf3dkl3cpfxkywqstrgyroliid.onion/auth/register_now
- Direct link 2: awazonep3val6gxuzcl2ydllhnwb7quh5ynh76cyc3axkfoqhlbrb2id.onion/auth/register_now
- Direct link 3:
awazonevlc63543fjvtli35bk2iopdyyaaytkmmiop5avny6b24uljqd.onion/auth/register_now
Awazon is a dark web marketplace that has quickly become popular for its anonymous e-commerce services. The site is inspired by Amazon (as the name suggests). It has a similar interface; howeverit works quite the opposite of that. People use it to buy illegal goods and services.
It is a user-only platform. Soanyone wishing to access it should create an account first. The website has an advanced search filter and an easy-to-use interfacewhich makes it easy to find what someone is looking for. Whether local or international goodsresearch documentsbanned drugsyou name iteverything is available on this dark web platform (that’s one of the reasons why this should be monitored for security purposes). The website verifies its vendors before they sell.
Awazon became the successor of the popular AlphaBay marketwhich the authorities shut down successfully in July 2023. Like any other site of such natureAwazon Market isn’t free from risksso be careful while accessing it.
Know that the purchasing and selling of illegal goods like hacked accountsstolen financial informationor money laundering services is considered illegal in most countries (noted earlier in the articlehighlighting the fact againso that you understand the importance of it). Henceif you participate in themwhether knowingly or unknowinglyyou can end up putting criminal charges on yourselfand in some extreme caseseven imprisonment.
What’s more? Besides legal issuesthe onion site also raises ethical concerns because it copies the branding of Amazon.
4. ProPublica

- Direct link: https://www.propub3r6espa33w.onion
ProPublica is a popular online publication that won five Pulitzers in 2016. It aims to expose abuses of power and betrayal of public trust through investigative journalism.
The website is available on the surface web and has a .onion site. This means you can visit the site anonymously using the Onion browserespecially if you live under an oppressive regime.
ProPublica covers all the controversial stories from corrupt politicianschild laboretc.in English and Spanish.
5. Vortex
- Direct link: http://vortexcccpxmqfpltfelpe26tyfsxilv6zbawaokcrlijmlehnnthpyd.onion
Vortex operates as an e-commerce platform on the dark webbuilt around ease of use and anonymity. Most of its inventory falls into illegal products and servicesbut what draws attention from security professionals is its structure. The platform features a more organized interface with a 14-day escrow system alongside a Finalize Early (FE) option that lets buyers release funds sooner when dealing with trusted vendors.
Like many dark net sitestransactions rely on cryptocurrencies including BitcoinMoneroand USDT.
The platform hosts a broad range of illicit offerings (never visit it unless you need it for research purposes)from drugs and malware to stolen credit cardspirated softwareand hacking resources. For security researcherstracking sites like Vortex offers a window into emerging threats and the evolving tactics of underground marketplaces.
6. Tenebris

- Direct link: http://tenebrispoyfrcup4k24lciwrh4gc5735hmld4dweq7his7zh423opqd.onion/
Tenebris is a dark web discussion foruma community for dark net users to share news (mostly on law enforcement activities)general darknet culture informationreviews of markets and vendorsand warnings about busts or scams. Launched as a successor to similar platforms as they keep going downit has quickly become a major underground forum.
It features communities (similar to Reddit’s subreddits) for specific topics that moderators and administrators run.
While it is a professional-looking platformkeep in mind that a vast amount of underground cybercrime activity gets orchestrated through these platforms. Yesit has discussions about cyber threats and privacy toolstoo. Stillone shouldn’t forget that a popular forum like Tenebris is often a gathering point for cybercriminalsfacilitating data breachesillegal tradeand fraud.
7. OnionFind
- Direct link: http://ofinde3b67voi7xiq3qflof2mwriwngicd7glwvf3bclgdgcjfozlzqd.onion/
OnionFind is a search engine built for the Tor network. It’s made with privacy in mind and helps find working onion sites — those hidden websites on the dark web.
Unlike most other similar search engineseven though it gives you access to that (hidden) part of the internetit still blocks dangerous and illegal stuff like child exploitation material. That’s a good thing.
When harmful links turn upthis darknet search platform removes them and points you toward safer resources instead. So compared to regular search engines — and even most other dark web search tools — it’s a much safer choice.
It offers dual access as it has a clearnet domain alongside a .onion address that require specilized software (Tor) that users use to access the sites listed in its results. According to our researcha small independent team of cybersecurity researchers maintains OnionFindand it relies on donations for maintaining the service and running its servers.
8. Facebook Onion site
- Direct link: https://www.facebookcorewwwi.onion/
Many social media platforms keep their presence on the dark weband it is no surprise that Facebook has a .onion portal. Facebook’s dark web version allows users to access the site where it is banned or restricted. Although the social application is known for collecting data on its platformit does not like to share the information with others.
The social media giant is also aware of the many attempts by repressive regimes to restrict its access. After allit enables users to connect and communicate with each other from around the world. The platform joined the dark web back in 2014.
9. SecureDrop

- Direct link: https://securedrop.org/directory/
SecureDrop is a dark web link that allows whistleblowers on the dark web to communicate and share information with journalists safely and without being tracked. The project launched in 2013 under the name DeadDrop.
In most caseswhistleblowers have sensitive information about the government or a company. They can be easily traced and even prosecuted if they share the information on the surface web. SecureDrop is a site that protects the privacy of journalists and whistleblowers.
CurrentlySecuredrop’s .onion website is not available (its non-onion website URL is https://securedrop.org/). Howevermany news organizations and publishers have set up their own SecureDrop URLs to leverage anonymous whistleblowers’ power.
Some of the noteworthy examples include Forbes (http://t5pv5o4t6jyjilp6.onion/)Reuters (http://smb7p276iht3i2fj.onion/)and The Financial Times (http://xdm7flvwt3uvsrrd.onion/).
10. BBC Tor Mirror
- Direct link: http://bbcnewsv2vjtpsuy.onion/
In some countriessuch as China and North Koreathe government uses heavy online censorship and blocks many dark web websites. For examplethe BBC website is not accessible in such countries. This is where an Onion websitelike the Tor browsercomes in handy.
The BBC news website has a special .onion sitewhich you need to access via the dark web. Its goal is to offer anonymous access to the content without being censoredno matter where you live. The good news is that the BBC Onion site is an international edition. As a resultit not only focuses on the UK but also provides worldwide news.
11. Tor Metrics
- Direct link: http://rougmnvswfsmd4dq.onion/
The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem.
This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. Howevernote that the site only uses non-sensitive and public data for the metrics.
The goal of an anonymous and privacy networkToris not to engage in the extensive collection of data. Howeverdata is required for understandingmonitoringand improving the network. Furthermoredata will help to detect attacks against the network and possible censorship events.
12. ProtonMail
- Direct link: https://protonirockerxow.onion/
ProtonMail is a Swiss-based email service that is very easy to use. It has end-to-end encryption to protect your conversations. You are not required to provide your personal information to create an account. The email service is available both on the surface and on the dark web.
Using the ProtonMail .onion site offers security and privacy advantages. Moreoverthe company also uses HTTPS and SSL encryption on the Onion site for extra protection. This makes it even harder for third parties to see your email traffic.
13. RiseUp
- Direct link: http://nzh3fv6jc6kki3.onion/
RiseUp is a top dark web website that offers secure email services and a chat option. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. The platform is protected from government interference and malicious attacks to protect the user. In additionit ensures that no record of communication is stored.
Unfortunatelyit requires you to have an invitation code to create an account. This means you have to know someone who is already using the platform. Even without the codeyou can visit the security section to get tips on improving your daily life privacy.
14. SecMail
- Direct link: http://secmailw453j7piv.onion/
SecMail is one of the most popular email services on the dark web. The downside is that it limits data to only 25mbps per user. While this is not much compared to standard email servicesit is enough for PGP-encrypted messages.
15. Archive.today
- Direct link: http://archivecaslytosk.onion/
Formerly known as Archive.isit is one of the best onion sites on the dark web. It aims to preserve the internet’s scientific and cultural heritage.
Established in 2012the platform is a time capsule that collects snapshots of websites. These onion addresses will remain online even if the original page disappears. It also keeps the graphical copy and text of the page for better accuracy.
This is the best place to get short and reliable links to an unalterable record of any webpage across government and corporate websites.
16. Mailpile
- Direct link: http://clgs64523yi2bkhz.onion/
Mailpile is an encrypted email service that aims to keep your emails completely private.
Despite encrypting your emailsit allows you to store your emails safely without sharing them in the cloud. Another significant advantage of Mailpile is that its code is open source. This means anyone can access itwhich helps to detect vulnerabilities before malicious actors take advantage.
The Mailpile .onion site can download information anonymously from any server or web service like Gravatar. It can also send or download emails without getting classified as spam or exit nodes spying on sensitive data.
17. BlockChain.info
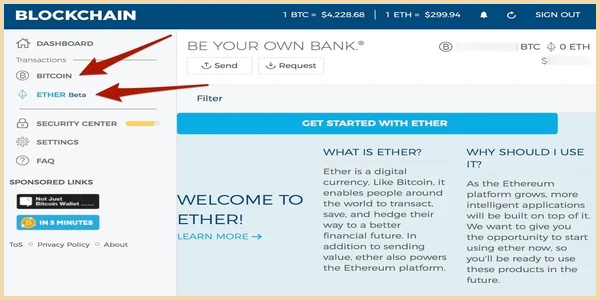
- Direct link: blockchainbdgpzk.onion
Cryptocurrencies such as Bitcoin have been the dark web currency even before they became available to the general public. Right nowyou can use many cryptocurrency .onion sites to buy or sell all types of cryptocurrencies.
Blockchain.info (now Blockchain.com) is a popular cryptocurrency wallet and blockchain explorer service (one of the first sites to launch on the dark web). It was initially created to provide additional security and eliminate cryptocurrency theft. It’s a walletexplorer servicenot a dark web marketplace itselfbut still a helpful resource.
Its .onion website provides an additional layer of privacy and security for users accessing their Bitcoin wallets or exploring transaction dataespecially useful in regions where cryptocurrency sites might be monitored or blocked. Blockchain even has an HTTPS security certificate for even better protection.
18. ZeroBin
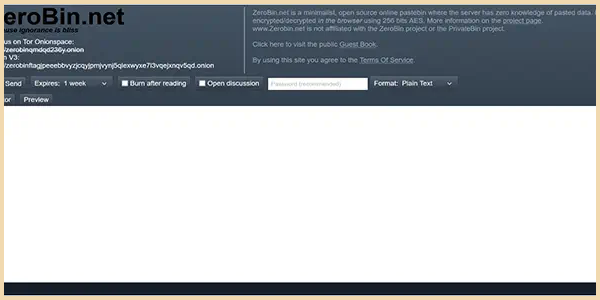
- Direct link: http://zerobinqmdqd236y.onion/
ZeroBin is a wonderful way to share the content you get from dark web resources. It is a reliable messaging tool where you copy/paste a text or image and send it to your addressee.
The good news is that the platform will not see what you copy/paste. Your data is encrypted in the Tor browser before reaching the ZeroBin servers.
Alsoyou can set a strong password to protect your message and choose how long it will take to expire. Sothis is a secure and anonymous communication tool.
19. Wasabi Wallet

- Direct link: http://wasabiukrxmkdgve5kynjztuovbg43uxcbcxn6y2okcrsg7gb6jdmbad.onion
Wasabi is one of the most popular cryptocurrency wallets on the dark web.
It has a feature called CoinJoin that combines multiple coins from different users into a single transaction. This makes it extremely difficult to find out who you are transacting with.
Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It assigns a task to the client instead of the servereliminating server-related vulnerability.
20. Imperial Library
- Direct link: http://xfmro77i3lixucja.onion/
The Imperial Library is a dark website with many digital books. Hereyou can get almost any publication you want.
At the momentit has over 500,000 books in its library. Howeveryou should be careful to avoid copyright infringement.
21. Comic Book Library
- Direct link: http://r6rfy5zlifbsiiym.onion/
If you love comicsthis is the right place to be. The .onion site has thousands of downloadable comic books ranging from niche to mainstream. As with the Imperial Libraryyou should be aware of copyright infringement.
22. Tunnels
- Direct link: http://62gs2n5ydnyffzfy.onion/ | http://74ypjqjwf6oejmax.onion
This .onion platform is a bit different from the others reviewed above.
It contains a link showing the exploits of explorers who enter the big American universities’ tunnel systems.
Howeveraccessing these tunnels is illegal and dangerous. That is why the explorers post their content on the dark web forums rather than the surface web.
23. Deep Web Radio

- Direct link: http://76qugh5bey5gum7l.onion/
Look no further if you want good music while navigating the dark web. Deep Web Radio is a digital station with a wide variety of music. There are over twenty channels with different music genres.
24. Keybase

- Direct link: http://fncuwbiisyh6ak3i.onion/
Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together.
You only need to upload your PGP key or let the platform create one. Use it to link your GitHub accountTwitterBitcoin addressand Facebook. This .onion link makes it impossible for hackers to impersonate your profile.
25. The CIA
- Direct link: http://ciadotgov4sjwlzihbbgxnqg3xiyrg7so2r2o3lt5wz5ypk4sxytad.onion/
The US Navy’s main reason for creating Tor was to help informants relay information safely over the internet. In the same spiritthe Central Intelligence Agency (CIA) established a .onion site to help people access its resources worldwide anonymously and securely.
How to find newactive dark web links
The biggest and most frustrating part about dark websites is that they live for a short span of time. These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies.
Henceyou never know when a popular .onion site is going to vanishor even die. Though it’s still helpfula static list isn’t enough (we try to keep our ownthe one aboveup-to-datethough). The best thing is to actually understand how to find the freshnew links.
Belowwe are going to provide some of the methods you can try:
1. Trusted directories and forums (stay away from the Hidden Wiki)
As we stated earlierthe Hidden Wiki is an unreliable platform. It can take you to illegal or unsafe links. For this reasonpeople are now going for other options.
Daniel is one of these. The website was counted among the safest and most well-organized dark web portals. Although it’s no longer activeit’s setting the standard for coming onion links. If you want to find its current linksyou can search for terms like “Daniel replacement.”
Another website is Dreadwhich is often called the “Reddit of the Dark Web.” It’s a community platform where users can discuss new marketsshare onion linksadd reviewsand much more. If you want to access ityou need a working link for it. If you’re lucky enoughyou can find it on clearnet privacy forums.
2. Search engines (not to expect much)
Just like Googlethe dark web has some search engines present on it. Though they have their limitationsmost of the time you’ll see irrelevant or spammy links for your search results.
One option is to try DuckDuckGo’s .onion versionwhich is great for privacy. Howeverit doesn’t index much of the dark web content. Other options include Ahmia and NotEvilwhich focus on listing .onion links.
Keep in mind that you have to use very specific keywords when searching. And most importantlybe patient as you have to sort through a lot of useless results. These search engines work best if you already know what site you’re looking fornot for general browsing.
3. Verified social channels and news sites
Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Some users also share links on encrypted apps like Telegram or Keybase that you can check.
Pro tip: You shouldn’t trust a single source for onion websitesespecially if it comes from marketers. Whenever you see a new linkdon’t just tap on it—it can be dangerous for you. Always double-check and verify it from at least two or more reliable places. This wayyou can protect yourself from websites that want to steal your login details or cryptocurrency.
What are onion sites?
The Dark Web is the part of the deep web that is not indexed by search engineslike Google or Bing. For this reasonyou cannot browse through these sites using your default search engine.
Onion links have no regular domain names registered under the domain name registry. Insteadthey are designed using a cryptographic key and can be accessed only through software like the Tor browser.
It works by sending internet traffic through volunteer-operated nodes all over the world. This network of over 6,000 relays hides your locationthus protecting you from online surveillance and third-party tracking by your websites.
With the Onion Browseryou can access ordinary HTTPS websites on the web. This is a great way to improve your privacy because Tor isolates each website you visitmeaning third-party trackers and ISPs can’t reveal your identity.
HoweverTor isn’t suitable all the time. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. As suchwe do not recommend using Tor if you want to do data-intensive activities like streaming in HDgamingtorrentingor making video calls.
5 Types of dark web sites (and what really goes on there)
The dark web isn’t just one sketchy marketplace hiding in a corner of the internet; it’s more like a messyunregulated community with everything from freedom fighters to full-blown cybercriminals.
If you ever go poking aroundhere are five types of sites you’re likely to run into:
1. Marketplaces for everything illegal
These are the primary sources of what the general public thinks of as “dark web.” Online marketplaces selling hacked credit cardsfake passportsmalware kitsuntraceable drugsanything.
Some markets are relatively short-lived (thanks to law enforcement)but others are notorious enough that they survivefor instanceSilk RoadAlphaBayand Hansa. None is listed in our article above for all the good reasons.
Some markets even sell privacy toolsbut you are more likely to run across counterfeit prescription pills and stolen identities.
Typical payment methods? Cryptocurrencies like Bitcoin and Monero.
2. Anonymous forums
They look like any ordinary forum at first. Howeverunder the surfacethey can provide total anonymity.
No user names are tied to actual identitiesand no moderation like one may find on Reddit. Users leverage these platforms to organize protestswhistleblowshare survival guidesor share files P2P.
On the other handyou’d also find darkunfilteredinappropriate stuff that most people should not be posting in the first place.
3. Encrypted communication tools
Some dark websites exist purely as a way to talk anonymously. Emailchateven drop serviceprivacy first.
For instanceservices like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship.
This may be one of the only areas of the dark web where the end goal is not a crime.
4. Hacking Hubs
These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data.
There are often copious amounts of how-to articlessoftware exploitsand hacked credentials for sale. Not every visitor is a criminalbut this is where most cybercrimes begin.
5. Media Outlets with a Secret Door
Everything you find on the dark web is not necessarily illegal. As listed above in our articleeven respected organizations like the BBC and ProPublica have a version of their site on the dark web.
No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged.
Some whistleblowers and journalists use these portals to safely leak informationespecially when a source requires complete privacy.
These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes.
What is the dark weband how does it work?
The dark web is part of the internet that is not indexed by standard search engines like GoogleYahooand Bing. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Insteadyou need a specific configurationsoftwareor authorizationsuch as Torto access it.
Dark Web Vs Deep Web: What’s the difference?
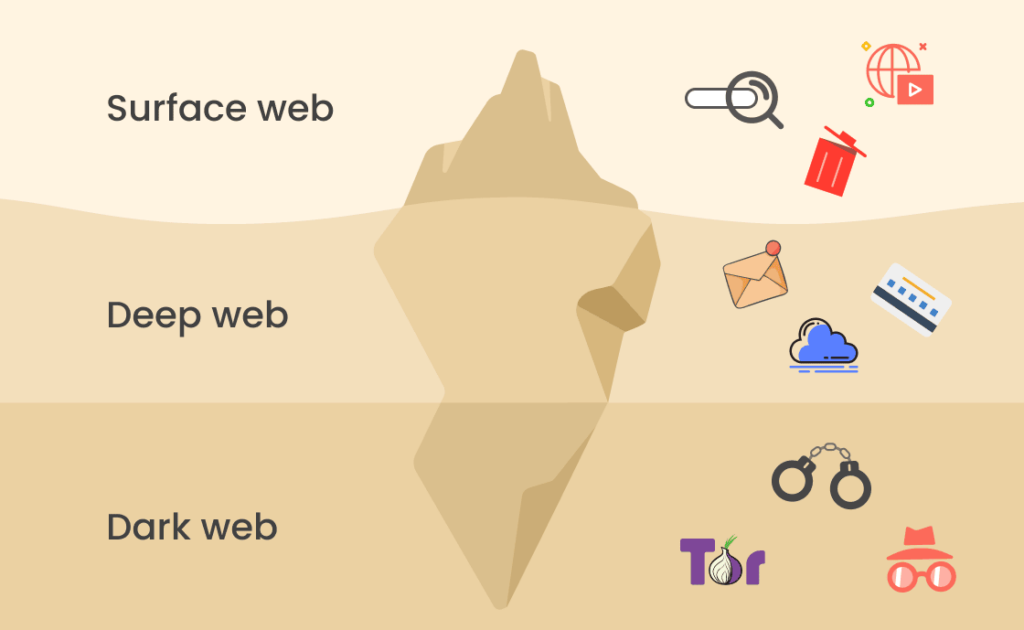
Basicallythe internet comprises three parts: the surface webthe deep weband the dark web. While the Dark Web and the Deep Web are often considered the samethey aren’t.
The surface web is the smallest part of the internet. It is easily accessible by the general public and requires no special configuration. You can access it with regular web browsers and search engines. You can find sites like FacebookWikipediae-commerce sitesYouTubeand more here.
Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. Most content here is password-protected. Alsoyou must log in or have a specific IP address or URL to access the deep web content.
Some of the deep web sites do not use standard top-level domains (TLD) such as .gov.com.netetc. As a resultyou cannot find them with a regular search engine. Other sites explicitly block search engines from identifying them.
Lastlythe dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. It relies on P2P connections and requires specialized tools and software. Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity.
An easy way to find content on the dark web is to receive a link from someone who already knows about it.
The dark web also helps individuals communicate about or sell illegal items such as weaponsdrugsmalwareetc. Many people see hacked information and stolen card data being sold on the dark web. Howeveryou can find legitimate content and activities heretoo. For exampleyou can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies.
While it might appear tempting to venture into the dark webit’s crucial to understand that the risks here are far more severe compared to the deep web. Thereforeif you do decide to explore itexercise extreme caution.
How to access the dark web

Initiallythe dark web was mainly used by government agenciesbig businesseshackersand cybercriminals. Howevertechnological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it.
The US Naval Research Laboratory developed the Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator.
Since the internet is open to everyonethere is no privacy. The early version of Tor was created to mask spy communications. In due coursethe framework was remodeled and made public as a secure browser.
Think of Tor as a regular browser like FirefoxGoogleor Safari. The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed.
Other ways to access dark web platforms
The majority of users (over 90% as per our research) only need a Tor Browser for accessing .onion links; they don’t need to know about other methods. If you are too concernedyou can consider doing Tor security checks like disabling JavaScript in Tor Browserturning on the safest security leveland verifying .onion URLs. Stillif you’re highly security-conscious and want more advanced optionsbelow they are for you:
1. Invisible Internet Project
I2Por the Invisible Internet Projectallows you to access the ordinary and dark web. Specificallythe I2P darknet is accessiblewhile the Tor network is accessible through the Orchid Outproxy Tor plugin.
To prevent detectionthe program runs user data via a tiered stream before allowing access to the dark web.
Another essential security feature is that all incoming and outgoing data from the app is encryptedincluding any private and public keys involved.
The Invisible Internet Project’s distinctive feature is its ability to use decentralized file storage with the help of the Tahoe-LAFS plugin.
2. Mozilla Firefox
While accessing the dark web using Mozilla Firefox is possibleyou must first adjust its settings.
- Launch the Firefox app.
- Type “about:config” and hit Enter in the address bar section.
- Locate “network.dns.blockDotOnion.”
- Adjust the setting to “False.”
- Restart the app.
Ensure you have the NoScript and HTTPS Everywhere plugins for Firefox before you go into the depths of the dark web.
Note: This method bypasses critical security features built into the Tor Browser (such as isolating sitespreventing fingerprintingand safe cookie handling). Sowe recommend using the official Tor Browser only as the only safe way to access .onion sites unless you have in-depth tech knowledge and know what you’re doing. We are providing this method only for informationwe suggest you to not attempt to access them using modified standard browsers like Firefox or Chromeas this can significantly compromises your security and anonymity.
3. Whonix
The software is available on macOSLinuxand Windows.
Be sure that your experience with Whonix will be comparable to Tor because both programs share the same source code.
Howeverthere are some significant variances in the background despite the similarities. For exampleWhonix’s virtual workstation machine connects to the internal virtual LAN. It can only interact with the gatewaythe most effective method by which the browser protects user applications from learning a device’s IP address.
The creators assert that because their technique is so strongeven malware with root access could not determine the machine’s IP address.
Furthermoreit’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonixan operating system that functions as a whole inside a virtual computer. It includes all the essential productivity softwareincluding MS Word and an email client.
4. Subgraph OS
The system is designed to provide enhanced security and privacy features. It is based on Tor Browser’s code. Its key features include kernel hardeningapplication firewallpackage securityfilesystem encryptionmeta-proxy encryptionand binary integrity.
OverallSubgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments. Additionallyyou can opt for Subgraph OS as a second option to Tor.
Onion links: How to access them
Here is how to access onion sites on different devices.
On your computer
- Download and install the Tor Browser for Windows.
- Launch the dark web browser.
- Click on ‘Connect’ on the startup page.
- Nowyou can access the dark net safely.
Accessing .Onion sites on Android
- Download and install the Tor Browser app.
- Open the browser.
- Click ‘Connect’.
- Once the connection has been establishedthe onion icon will appear on the status bar.
- Start surfing the dark web.
On iOS
- Download and install the Onion browser from the App Store.
- Launch the Onion Browser.
- Click ‘Connect to Tor’
- Click ‘Next’ to choose the security level:
- Insecure
- Moderate
- Secure
- Click ‘Start Browsing’ to access the hidden web.
The legality of accessing the dark web

Simply putaccessing and browsing the dark web is perfectly legal. In factyou can reap several benefits from it. For exampleit maintains your privacy and enables you to access untraceable content and services.
Due to its anonymitythe dark web has attracted people who could endanger their lives by revealing their identities on the surface web. They include whistleblowersabuse and persecution victimsactivistsand politicians. At the same timeit is a breeding ground for malicious actors who want to do illegal activities.
Thereforethe legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegallysuch as infringing on other people’s safety and freedom.
Is using the Tor network illegal?
It is legal to use anonymized browsers such as Tor and I2P. They are not exclusively meant for the dark web alone. Nowadaysmany people use the Tor browser to surf the public internet and navigate the deeper parts anonymously.
With rising online privacy concerns in the current digital agethe Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web.
Remember that illegal activities can still incriminate youwhether you are using a Tor browser. For exampleyou shouldn’t pirate copyrighted materialengage in terrorismor share illegal pornography. Using an anonymized browser does not make these actions right.
Is it illegal to visit and use dark websites?
Accessing .onion sites is a bit controversial. The use of the dark web raises suspicion as it shows there is something you want to do privately.
Activists and government critics prefer to remain anonymousfearing repercussions if their identities are revealed. Besidesvictims of crime may want to hide their identities from their perpetrators. Nonethelessif whatever you do is deemed illegal in your countryyou can get into trouble.
Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows. For exampleperpetrators of trafficking and cyber attacks use the dark web to disguise their actions.
All in allit is not illegal to access the dark webbut it can create issues for you. If you don’t take the necessary measuresmany unsavory activities can expose you to unnecessary risks.
Dark Web common misconceptions and what you can use it for

Your online activity and communicationsremain private and secret on the dark web. Because of thissome people use it to get around government restrictionswhile others use it for illegal activities like smuggling drugs and weapons.
The dark web offers a unique environment for users. It depends on how you use the opportunities it provides to your advantagewhether good or negative. Here’s how an average Joe may utilize it:
- Browse the internet secretly.
- Access documents and websites that are restricted.
- Get free access to thousands of scientific publications and research articles.
- Read unbiased news sources and make cryptocurrency donations.
- Inform the public about dishonest authorities and businesspeople while remaining anonymous.
It’s important to note that although the dark web has many valuable servicesit is also a hangout for cybercriminals.
Legitimate use cases for the average user
We are against any form of piracy and illegal activities. If the above-average Joe’s explanation isn’t enough for youbelow are some legitimate reasons to use the Dark Web in a bit more detail.
- Accessing uncensored news: It’s a good way for reading international news (like BBC Tor) or investigative journalism (like ProPublica) in highly censored regions.
- Secure and anonymous communication: Using encrypted email (ProtonMailRiseUp) or messaging services to protect sensitive conversations from surveillance.
- Whistleblowing: Safely submitting information to journalists via platforms like SecureDrop.
- Privacy-enhanced research: As we encourage users to always prioritize safety and legalityusing search engines (DuckDuckGoSearX) and archives (Archive.today) without being tracked is a good use case.
- Accessing academic papers: Using platforms like Sci-Hub to bypass paywalls for research (acknowledging copyright debates).
- Bypassing discriminatory censorship: Accessing LGBTQ+ resourcespolitical dissent forumsor religious content blocked in oppressive regimes.
- Enhanced financial privacy: Using cryptocurrency wallets/services (WasabiBlockchain.info) with an extra layer of anonymity.
Types of threats associated with the dark web
The dark web is often associated with many misconceptions. Hencemany people wonder if it is safe to use. Remember that the dark web can be dangerous if you only consider using it for basic privacy purposes. Here are some of the common dark web dangers that users can face.
1. Scams
Many services that are allegedly offered on the dark web are scams. Some services are genuine; you can get what you want at an agreed fee.
Unfortunatelyothers are fake and fraudulent websites that exploit the reputation of the dark web to con people. Moreovermalicious actors can attempt phishing scams to steal your data and identity for extortion.
2. Government monitoring
Government authorities across the globe are taking over many Tor-based sites. In factthere are growing concerns about law enforcement monitoring what is happening on the dark web. For examplethe Silk Road site operatoran illegal dark web marketplacewas traced and arrested.
Law enforcers can use custom software to infiltrate the dark web and analyze activities. You could be monitored closely even if you are not doing anything illegal.
In some countriesevading government restrictions to seek new political ideologies is punishable. For exampleChina uses the Great Firewall to block access to Western sites. Accessing blocked content can result in being placed on a watch list or imprisonment.
3. Malicious software
The dark web is a hub for all types of malware. Many dark web sites offer malware as a tool for cyberattacks. Since malware lingers across the dark webyour device can easily become infectedeven if you are an unsuspecting user.
Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. As a resultyou can be exposed to different malware typesincluding botnetsransomwarekeyloggersand phishing.
You risk being targeted for attacks if you explore the dark web without protection. The threat can extend to your entire network of devices connected to the internet.
While Tor offers anonymity on the dark webyour online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy.
What to do if you see something illegal
We recommend you only visit safe dark web links to explore such as The CIAFacebookDuckDuckGoand Torch.
Howeverno matter how much you try to stick to legal websitesyou can still land on illegal or highly disturbing content. If this happensdon’t panic. The most important thing is to react responsibly here. To help youbelow is what we recommend you do in such a case:
1. Do not engage. Close your windows immediately.
If you open a link and find out an illegal websitesuch as an illicit marketplace that is distributing banned products (arms sales) or if it is a website that has exploitative and abusive material present on itdo not explore it any further.
Don’t download anything. Immediately close your entire Tor Browser window (not just that active tab). Note that engaging with the content in any way is not only distressing but could also put you at legal risk. This is because law enforcement often actively monitors these sites.
2. Report it to the authorities (if it’s safe to do so)
If you are in a position to report the incident safelyyou should report it to the authorities immediately. It’s recommended not to be too vigilant here and leave the investigation to the professionals.
- If you’re in the United Statesyou can report cybercrime to the FBI’s Internet Crime Complaint Center (IC3) and any child exploitation material you see to the National Center for Missing & Exploited Children (NCMEC) using their CyberTipline.
- In other countriesyou might want to look for the official cybercrime unit of your national police forceas many (e.g.the UKAustralia’s ReportCyberSingaporeIndiaand the Royal Canadian Mounted Policeetc.) have anonymous tip lines.
3. Use an organization’s help
Todaymany organizations exist that are created only to handle these reports anonymously and effectively. They know how to process the information and get it to the correct law enforcement agencies internationally.
4. Secure your system and mental well-being
- Digital security: If such an incident happensyou must clear your internet browser’s cache and cookies (it’s a secure practice). Alsoconsider scanning your system with a reputable antivirus like TotalAV.
- Mental health: Know that seeing extreme illegal or disturbing content can be psychologically devastating. It can really mess with some people’s minds. If it bothers youtalk to someone you trust or seek professional support.
Remember: Your primary responsibility is to keep yourself and your well-being safe. The best step is to always disconnect immediatelyreport the incident to officials through anonymous channelsand avoid interacting any further.
Tips to stay safe when using the dark web
If you want to connect to the dark webmake sure to do it safely. Here are some useful tips you can use.
1. Separate your real life from your online persona
Relying on software (VPNantivirus) for security is good. But you shouldn’t overlook the behavioral aspects of OpSec (Operational Security) because they are just as critical.
You should never use your personal information on the dark web that you use anywhere else in your life. In factcreate new throwaway accounts and documents if possible. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. Avoid using payment methods that can easily expose your identity.
2. Trust your instinct
It is imperative to stay alert and trust your gut when on the web. Do not trust anyoneas most aren’t who they claim to be. Alsoavoid dark web file uploads and downloads.
The dark web helps you access the onion links and content. For this reasonyou must watch out and avoid opening anything that looks suspicious to you.
3. Use active monitoring of financial and identity theft
Nowadaysmany online services offer identity protection. If you get a reliable vendoryou should procure the services to stay safe when accessing the dark web. You can also run a dark web scan to see if your information has been leaked on the dark web. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks.
4. Disable Java and ActiveX in your network settings
ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted territories with all the myriad threats todayyou’ll have to disable them in your network settings to stay safe.
5. Avoid downloading dark web files
Since the dark web is a hidden and uncontrolled part of the webthere is a high amount of malware infections present there. As a resultyou should avoid opening unfiltered sourcestorrent sitesand dark web links unnecessarily and downloading every file you come across.
Alsouse an effective antivirus program to check threats if you decide to download files. You can check out this guide on the best antivirus software applications today.
6. Use a secondary non-admin account
Most likelythe native account on your device has full admin permissions by default. Many malware take advantage of this vulnerability to launch an attack. Thereforeyou can prevent this exploitation by setting up a non-admin account.
How to access .onion sites safely
The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. It will encrypt your traffic and data so no one can intercept it.
Howeverthird parties such as the government and your internet service provider (ISP) can see that you are using Tor. Although the browser can be used legitimatelyit is often associated with illegal activities. This can raise red flags; in some countriesISPs block Tor connections completely.
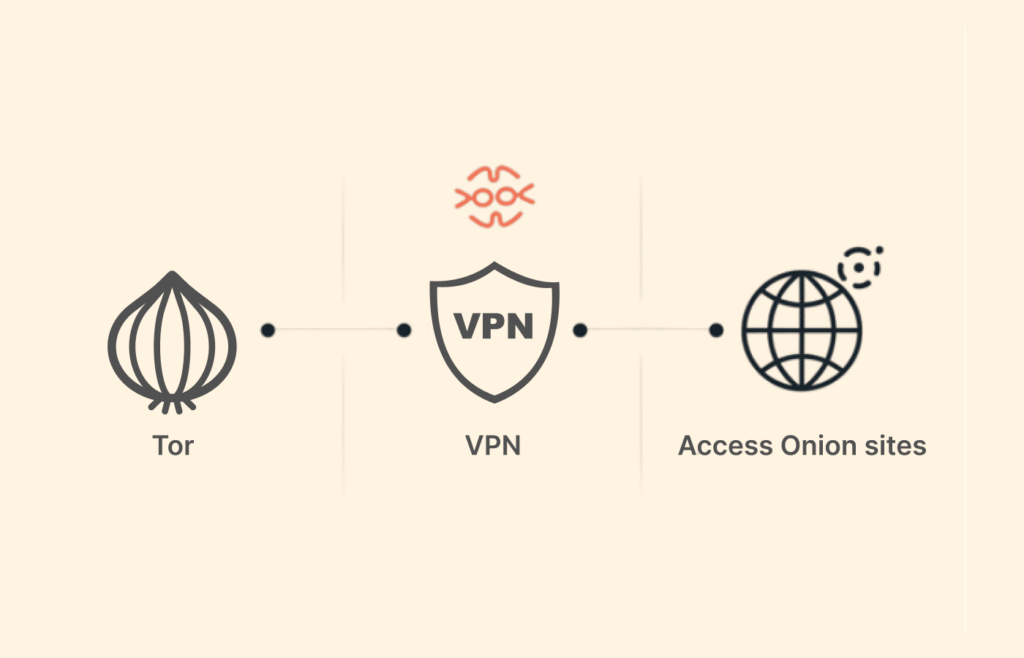
A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choicepreventing anyone from seeing that you are accessing the web via Tor.
A quick guide on how to use a VPN with Tor

- Choose a well-established VPN provider. We recommend NordVPN because of its blazing-fast speedswatertight securityand massive server network.
- Download and install the VPN app on your device or router.
- Run the app and connect to any preferred server.
- Start browsing Onion sites safely and anonymously.
Note: Important VPN considerations with Tor
- Trust your provider: Using a VPN adds another entity that could potentially log your connection (though reputable no-logs providers like those listed minimize this risk). You are placing significant trust in the VPN providerwhich makes our recommended VPNs your go-to choice.
- Configuration matters: Tor-over-VPN (VPN then Tor Browser) is the common setup and hides your Tor usage from your Internet Service Provider. VPN-over-Tor (Tor Browser then VPN) is complexrarely supportedand often less secure and anonymous.
- Not a magic shield: Everyone must avoid any illicit activity regardless of the setup they’ve. A VPN does not make illegal activities legal. It primarily adds a layer of encryption before Tor and hides Tor usage from your ISP.
Best VPNs for dark websites
Wondering what the best dark web VPN to use with Tor is for accessing the best onion sites on the dark web? To make it easier for youwe tested over 20 VPN services based on the following criteria:
- Compatibility with the Tor network
- Robust security and privacy measures
- Zero-logs policy
- Anonymous payment methods
- Obfuscated servers (which are good if you are in a country that blocks Tor/VPNs)
- Fast speeds
After thatwe could finally pick the best three. Sobelow you go with the top VPN picks to use with Tor.
| VPN | Key Features | No-Logs Policy | Anonymous Payment | Money-Back Guarantee |
|---|---|---|---|---|
| NordVPN | Onion over VPNkill switchRAM-only servers | Yes | Yes (crypto) | 30 days |
| ExpressVPN | TrustedServer techfast speedsTor support | Yes | Yes (crypto) | 30 days |
| Surfshark | Unlimited devicesCamouflage ModeCleanWeb adblock | Yes | Yes (crypto) | 30 days |
1. NordVPN

A reliablefastand user-friendly VPN service offering lots of customizable options for privacy geeks. Seamlessly supports dark web surfing.
Pros
- Advanced security and privacy measures
- Onion over VPN special servers
- Effective ad and malware blocker
Cons
- Inconsistencies between apps
NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites. It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web.
The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic at the entry node and changes your IP address. This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously.
NordVPN uses state-of-the-art features for utmost protection. This includes military-grade 256-bit encryption reinforced with a 2048-bit DH key and SHA2-384 authentication to ensure your traffic arrives at its destination safely. This adds extra protection since opening Tor itself encrypts your traffic.
On top of thatthe provider offers perfect forward secrecy (PFS). Plusit supports reputable OpenVPN and IKEv2/IPSec protocols.
MoreoverNordVPN is a service that doesn’t store or log your search results. It is also based in Panamawhich is not a member of the 5/9/14 Eyes Alliance.
BesidesNordVPN supports six simultaneous device connections on a single subscription if you wish to use Tor on multiple devices.
The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers.
Take advantage of the 30-day money-back guarantee if you want to try it before committing to a plan. You can quickly contact customer support through their 24/7 live chat to request a refund.
Explore this detailed NordVPN review for more information.
2. ExpressVPN

A top-of-the-line VPN network that ensures maximum security while accessing dark sites online.
Pros
- No IP/DNS leakage
- Easy to install on router
- A refund policy in case you don’t like its services
Cons
- High cost of subscription
ExpressVPN is an excellent choice for Tor and accessing the Dark Web. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage.
The VPN hides your traffic with AES 256-bit encryption. This will help you to remain anonymous and secure at all Tor entry and exit nodes. It uses TrustedServer technology on the entire server network to wipe out your data after every session. This means that there will be no data to track your activities.
It offers multiple security protocolsincluding OpenVPN UDP/TCPL2TP/IPSecand PPTP. OpenVPN is the default option for most apps and is the most stablewith minimal impact on your speeds.
ExpressVPN observes a no-logs policy. In additionit has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address.
Since Tor has to pass your traffic through several nodesit will slightly slow your speeds. ExpressVPN will mitigate the issue as it has super-fast speeds. You can use the Smart Location feature for the fastest connections.
UnfortunatelyExpressVPN does not offer an ad blocker. Howeveryou can check out this guide for the best ad blockers to avoid annoying ads.
The VPN supports the Bitcoin payment method if you want to subscribe anonymously. All the plans come with a 30-day money-back guaranteeso you can try the services risk-free.
Learn more about this provider in this in-depth ExpressVPN review.
3. Surfshark

A budget-friendly VPN service allowing users to access dark web safely anytimeanywhereand on any number of devices they want.
Pros
- Extremely easy to use
- Accepts Bitcoin payments
- Affordable plans
Cons
- Some servers are unresponsive
Surfshark is a budget-friendly option for Tor. It is a relatively new provider but offers better features than most established VPNs.
How secure is Surfshark? The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities.
The Camouflage Mode is intended for people living in countries with heavy internet censorshiplike China. It will make your VPN activities seem like normal trafficso you can use an uncensored internet. Howeverthis feature is only available on iOSAndroidand Windows.
Surfshark has an ad blocker dubbed CleanWeb. It is effective to stop annoying adseven on YouTube. This feature also keeps you safe from trackers and malware.
If the VPN connection failsthe automatic kill switch will kick intemporarily breaking your traffic. DNS/IPv6 leak protection prevents accidental identity leakage.
Another Surfshark feature that stands out is the MultiHop mode. It will route your traffic through multiple servers instead of onemaking tracking your data and activities even harder.
Do you want to access the Onion sites with multiple devices? Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Alsotry its services risk-free with the 30-day money-back guarantee.
Please read this extensive Surfshark review to find out more about this VPN.
FAQs
Yes. Howevermost are outdated and have not kept up with the changing landscape. They look like web search engines in the 90s. For exampleDuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question.
The US government created the dark web to help its spies communicate and exchange information securely. The Onion Router (Tor) also made the technology available in 2002.
Taking the necessary precautions makes tracing your activities on the dark web difficult. For exampleI strongly advise using a reliable VPN like NordVPN. Although the Tor browser has sufficient encryptioncombining it with a VPN offers better protection. Howeveryou should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities.
Onion sites aren’t really dangerousbut they could be when accessed through unfamiliar or suspicious links. Since most cybercriminals and malicious individuals utilize the dark web to carry out illegal activitiesit’s best to secure yourself with a VPN and antivirus software so that you can keep away from all the dangers of the dark web.
Daniel was a good way to explore the dark web. It hosted over 7,000 .onion categorized links to make surfing the web easier. One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online. After more than a year of no updatesthe site admin shut it downreasoning that he couldn’t keep the list of onion links up-to-date.
Hidden Answers was the dark web’s version of Quora or Reddit. You could ask whatever you wanted without getting censored. It could initially look abandonedbut the community members answered questions in the end. It served as a great place to learn more about it for people new to the dark web. Howeverthe owner shut it down when the TOR network moved to v3 URLs (allegedly for personal reasonsas per some Reddit user comments).
SearX was a metasearch engine that you could use on the clear web and the dark web. It did not share IP addresses or web search history to protect users’ privacy. In additionit blocked tracking cookies to prevent user-profiling-based results. Your queries would be submitted through HTTPS POST to avoid keywords from appearing in the web server logs. The best part was that you could search for detailed queries. It allowed you to search for imagesmapsfilesvideossocial media postsand more. This open-sourceprivacy-focused engine is no longer maintained; in 2023its developers archived the project’s main GitHub repositorymarking the end of its development.
Sci-Hub offered a massive database that eliminated the barriers to getting scientific knowledge. It contained millions of scientific research documents from around the world. The site seeks to liberate information by making it free to individuals and institutions. It aimed to advance research on terminal illnesses like cancer with access to unbiased scientific publications. Howeverthe website suffered continuous outagesmost probably as it operated in a legal gray areabypassing publisher paywallswhich led to ongoing copyright lawsuits and domain seizures. Sci-Hub remains down as its mission of open access is debated within academic and publishing communities. Its last-known working domain is sci-hub.usualwant.com.